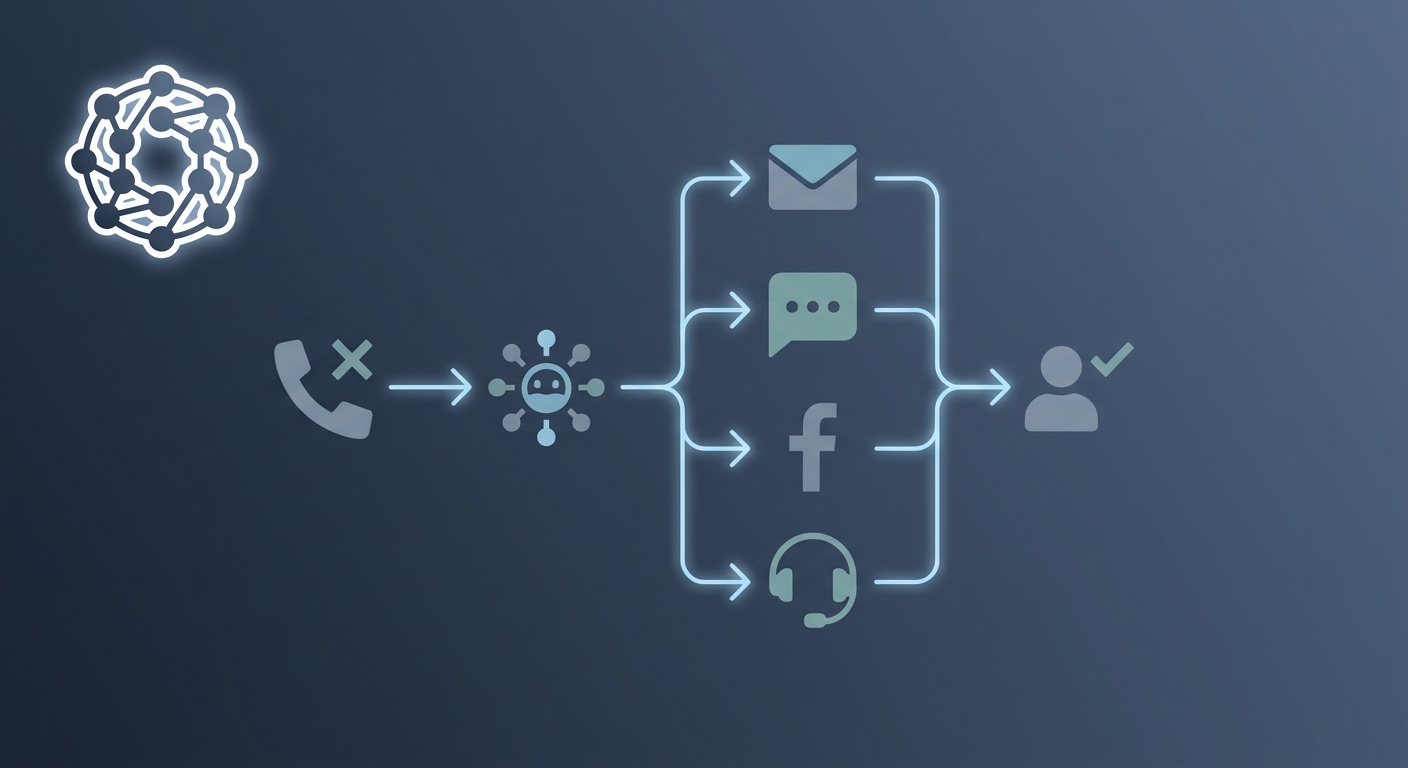
Automated omnichannel fallback workflows for missed inbound lead conversion
TL;DR
- This article covers how to build a bulletproof system for catching every missed call using ai and automated messaging. You will learn the exact workflows for routing calls intelligently, comparing the costs of ai vs human receptionists, and setting up instant sms fallbacks so your leads never go to a competitor while you are busy.
Why static mfa is failing in the modern world
Ever wonder why your "secure" login feels like a leaky bucket? We keep building bigger gates at the entrance but forget that once someone's inside, the gate don't matter anymore.
The biggest issue is that traditional systems only check who you are once. You pass the MFA, you get a session cookie, and you're good for eight hours. But what happens if that cookie gets swiped five minutes later?
- Session hijacking: Stolen cookies via malware happen after the login is done.
- Insider threats: A legit user starts dumping the entire database at 3 AM.
- aitm attacks: Real-time proxies relay your code and steal the session immediately.
According to Deepak Gupta, 60% of phishing-related breaches in 2025 now use techniques that bypass traditional mfa entirely. (Modern Authentication Trends Beyond Traditional MFA - 1Kosmos)
We gotta stop treating identity like a one-time event and start looking at it as a continuous stream. Next, let's look at how we actually move toward that "never trust" model.
Understanding the ai risk engine and scoring
So, how does the system actually "know" you're you? It's not magic, it’s just a ton of math running in the background. The ai risk engine basically acts like a digital bouncer that never sleeps, constantly crunching signals to see if things look fishy.
Most systems use a formula to calculate a risk score (R) in real-time. According to Hitarth Shah, this involves weighting factors like user behavior (U), device health (D), and external threat intelligence (T).
- Geolocation: If you log in from New York and then from London sixty minutes later, that "impossible travel" signal spikes your score.
- Device Posture: Is the laptop running an unpatched OS or missing its mdm profile? That’s a red flag in a zero trust model.
- Network Reputation: Requests coming from a known Tor exit node or a datacenter ip usually get extra scrutiny. (The risk to Tor exit nodes - Information Security Stack Exchange)
To keep things private and fast, a lot of these engines now use "edge processing." Basically, the raw data about your typing or location stays on your device or a nearby server, and only the risk score gets sent to the cloud. This helps with gdpr because you aren't shipping sensitive bio-data across the world.
"The likelihood that an auth attempt is malicious is modeled as a probability based on the deviation from your established baseline." — Hitarth Shah (2025).
Once the score is cooked, the system picks a path. As Authgear explains, this keeps the experience smooth for regulars while making life hard for hackers.
- Allow: Your score is low. You’re on your usual MacBook at your house. No friction, just get to work.
- Step up: Things look a bit weird—maybe a new browser. The system triggers a fido2 biometric check or a push notification.
- Block: Score is off the charts. The session is killed immediately, and secops gets a ping.
Honestly, it’s about balancing security without annoying your users to death. Next, let’s dig into how behavioral biometrics tracks how you actually move your mouse.
Behavioral biometrics as the secret sauce
Think about it—how many times have you approved a push notification without even looking? We’re all guilty of it. That’s why behavioral biometrics is such a game changer; it doesn’t ask for your permission, it just watches how you work.
This isn't about your fingerprint or face. It’s about the "how." Every person has a rhythm. According to Avatier, organizations using these AI-driven methods can slash account takeovers by 50% because the security is basically invisible.
- Keystroke Dynamics: The timing between "A" and "S" on your keyboard is unique. If a script or a different person takes over, the cadence breaks.
- Mouse & Touch: On mobile, things like grip angle and swipe pressure are tracked. If a bot tries to navigate, the movement is usually too "perfect" or linear.
- SSOJet & CIAM: Modern stacks use these data points to manage complex digital experiences without making users jump through hoops.
The "cold start" problem is real, though. You can't detect a deviation if you don't have a baseline. Most systems need about 5 to 15 sessions to "learn" you. During this learning phase, the system defaults to a "high-caution" mode—meaning you'll probably see more standard MFA or "Step up" challenges until it's sure about your patterns.
Honestly, it’s about making things easier for real people while making it a nightmare for bots. Let's look at the actual math and code that makes this happen.
The technical framework for ai-driven adaptive authentication
Building a framework that actually works requires moving past simple "if-else" logic. You need a system that weights different signals based on how much you trust them in a specific context.
The core of the framework is the risk score (R). We calculate this by aggregating the weighted factors: R = (w1 * U) + (w2 * D) + (w3 * T). Here, U is user behavior, D is device health, and T is threat intel. Each 'w' is a weight you assign based on importance. The result is a normalized value between 0.0 (totally safe) and 1.0 (definitely a hacker).
To keep things accurate, engineers use a probabilistic model. You're basically minimizing the mean squared error between your training data and real-world login outcomes.
Here is a quick look at how you might handle the initial entry point in a python-based api gateway.
def assess_auth_risk(user_context, risk_score):
# threshold set based on sensitivity of the app
THREAT_THRESHOLD = 0.75
<span class="hljs-keyword">if</span> risk_score > THREAT_THRESHOLD:
trigger_step_up(user_context.<span class="hljs-built_in">id</span>, method=<span class="hljs-string">"fido2"</span>)
<span class="hljs-keyword">return</span> <span class="hljs-string">"CHALLENGE_REQUIRED"</span>
<span class="hljs-keyword">elif</span> risk_score < <span class="hljs-number">0.3</span>:
<span class="hljs-keyword">return</span> <span class="hljs-string">"ALLOW"</span>
<span class="hljs-keyword">else</span>:
<span class="hljs-comment"># middle ground for suspicious but not certain threats</span>
trigger_step_up(user_context.<span class="hljs-built_in">id</span>, method=<span class="hljs-string">"push_notification"</span>)
<span class="hljs-keyword">return</span> <span class="hljs-string">"STEP_UP"</span>
This code is just the "front door" check. In a real Zero Trust setup, you run a similar check—often called Continuous Adaptive Trust—on every sensitive api call. If a retail user suddenly starts bulk downloading customer lists mid-session, the risk score spikes and the system kills the token immediately. Honestly, it's the only way to stay ahead of session hijacking.
Implementation roadmap and best practices
Building this isn't just flipping a switch—it’s more like tuning an engine while the car is moving. You gotta start with the plumbing. Before you even touch ai, make sure your signal ingestion is solid.
Don't go full "Minority Report" on day one. I've seen teams trigger massive alert fatigue by setting thresholds too tight.
- Phase 1: Just log data. See how users actually move.
- Phase 2: Run the engine in "shadow mode" to see what it would have blocked.
- Phase 3: Turn on enforcement for high-risk apps first, like finance or mdm.
Honestly, you need to watch out for gdpr when handling behavioral data. As mentioned earlier, process scores at the edge to keep things private. Also, remember that people change—a broken wrist changes how someone types. Your models need regular retraining so they don't lock out the ceo just because he’s tired.
According to Hitarth Shah, organizations see a 14% jump in detection accuracy when they stop relying on static rules. It’s a journey, but it beats getting pwned by a stolen cookie. Stay safe.